Palo Alto Networks Discloses Critical Firewall Flaw Under Active Exploitation, Urges Immediate Patching
Palo Alto Networks disclosed a critical buffer overflow vulnerability — tracked as CVE-2026-0300 — in its PAN-OS firewall software on May 5, 2026, confirming the flaw is already under active exploitation by threat actors who can use it to execute arbitrary code with root-level privileges on affected devices without any authentication, posing an immediate and severe risk to corporate networks, critical infrastructure, and government systems running the company's widely deployed security hardware.
Background
Palo Alto Networks is one of the largest cybersecurity companies in the world, with its next-generation firewalls deployed across tens of thousands of enterprise networks, government agencies, and critical infrastructure operators in the United States and globally. PAN-OS, the operating system that runs on those firewalls, is a high-value target for nation-state hackers and criminal groups precisely because compromising a firewall gives an attacker a privileged position inside a network — behind the very device designed to keep threats out.
The disclosure comes less than two weeks after the Cybersecurity and Infrastructure Security Agency ordered federal agencies to patch a separate Linux kernel vulnerability that had been under active exploitation. The back-to-back disclosures underscore the pace at which sophisticated threat actors are identifying and weaponizing vulnerabilities in foundational network infrastructure.
Key Developments
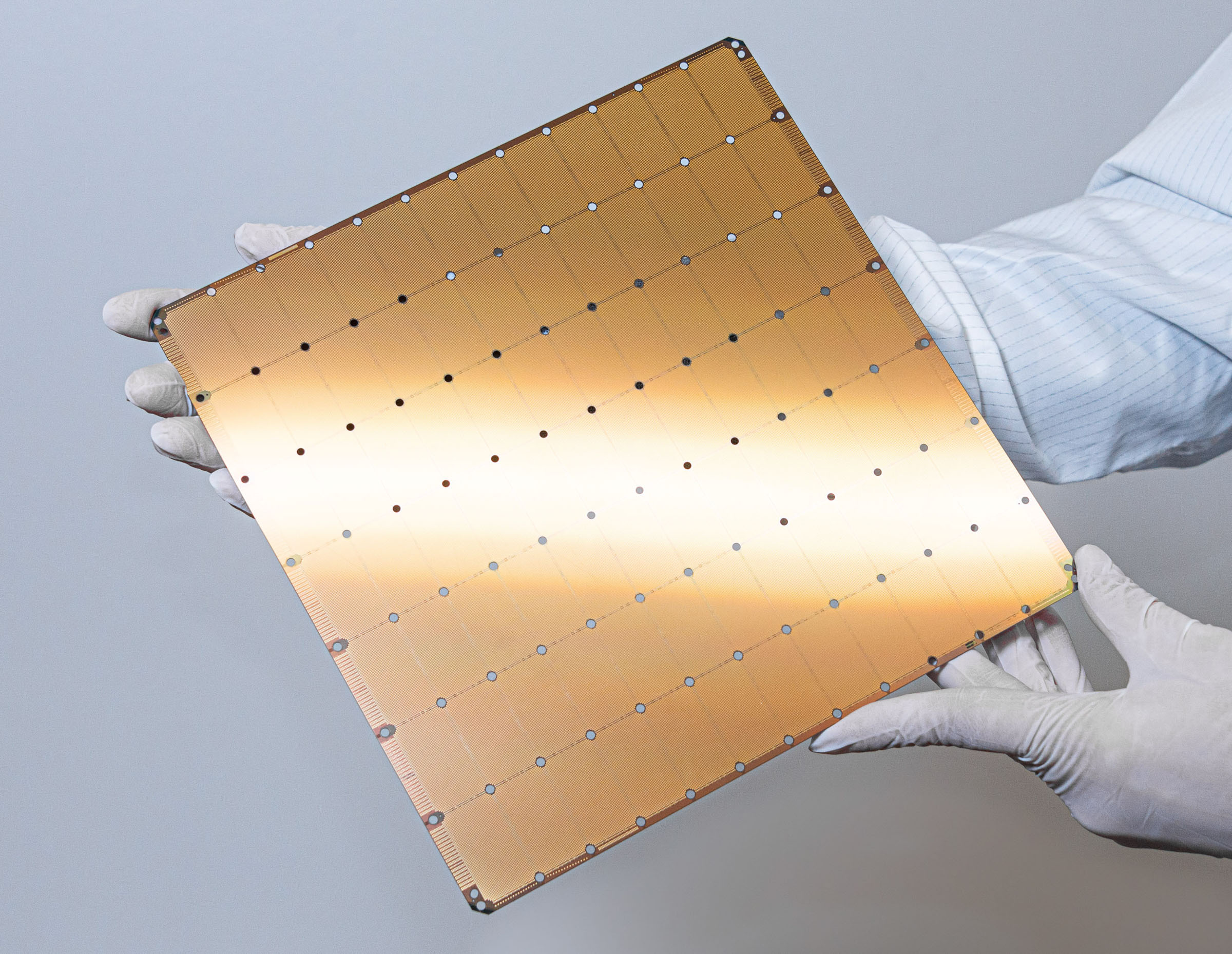
CVE-2026-0300 is a buffer overflow flaw in PAN-OS's GlobalProtect gateway component, which handles remote access connections for enterprise users. The vulnerability allows an unauthenticated attacker on the network to send a specially crafted packet that overflows a memory buffer, enabling arbitrary code execution with root privileges — the highest level of system access. An attacker with root access can disable security controls, exfiltrate data, install persistent backdoors, or pivot to other systems on the network.
Palo Alto Networks confirmed in its security advisory that the vulnerability is being actively exploited in the wild, meaning threat actors had already developed working exploit code before the patch was available. The company released PAN-OS updates addressing the flaw and urged all customers to apply patches immediately. As a temporary mitigation for organizations that cannot patch immediately, the company recommended disabling the GlobalProtect gateway feature, though doing so disrupts remote access for employees.
The Five Eyes intelligence alliance — comprising the United States, United Kingdom, Canada, Australia, and New Zealand — issued joint guidance on May 5 warning that the rapid deployment of networked security devices in enterprise environments has created new attack surfaces that traditional defenses are inadequate to address. The guidance specifically called out firewall and VPN appliances as high-priority targets for nation-state actors.
Why Americans Should Care
Palo Alto Networks firewalls protect networks across every sector of the US economy, from hospitals in Texas and Florida to financial institutions in New York and Chicago to energy infrastructure in the Gulf Coast. A successful exploit of CVE-2026-0300 gives an attacker the ability to bypass all downstream security controls — antivirus software, intrusion detection systems, and endpoint protection tools are all rendered ineffective once an attacker controls the firewall itself.
For federal agencies, CISA's standing directive requires patching of actively exploited vulnerabilities within 14 days for internet-facing systems. Agencies running PAN-OS across their networks — including the Department of Defense, the Department of Homeland Security, and the Department of Veterans Affairs — are under mandatory patching deadlines. State and local governments in California, New York, and Texas, which have large deployments of Palo Alto hardware, face the same urgency without the same mandatory framework.
Why It Matters
The CVE-2026-0300 disclosure follows a pattern that cybersecurity researchers have documented with increasing alarm: sophisticated threat actors, including groups linked to China's People's Liberation Army and Russia's GRU, are systematically targeting network edge devices — firewalls, VPN concentrators, and load balancers — as their primary initial access vector. A 2025 Mandiant report found that edge device vulnerabilities accounted for 36 percent of all confirmed initial access events in major breaches, up from 22 percent in 2023.
The strategic logic is straightforward: edge devices sit at the boundary between the internet and internal networks, they run proprietary operating systems that are harder to monitor with standard security tools, and they are often patched less frequently than endpoint devices because taking them offline disrupts business operations. The Palo Alto flaw exemplifies all three vulnerabilities simultaneously. Historically, similar flaws in Fortinet and Citrix products have been exploited by ransomware groups and nation-state actors for months before organizations completed patching — a timeline that the current disclosure's active exploitation status suggests may already be underway.
What's Next
CISA is expected to add CVE-2026-0300 to its Known Exploited Vulnerabilities catalog within days, triggering mandatory patching deadlines for all federal civilian agencies. Palo Alto Networks' threat intelligence team is actively working to attribute the exploitation activity to specific threat actors, with preliminary indicators suggesting involvement by a group with ties to a foreign government. Organizations that have not yet patched should treat any anomalous traffic through their GlobalProtect gateways as a potential indicator of compromise and engage incident response resources immediately.
Sources: The Hacker News; TechStartups.com; Palo Alto Networks Security Advisory