Vercel Security Breach Exposes Supply Chain Risks Across AI Developer Ecosystem
Vercel, a widely used cloud platform that hosts applications built by AI developers and startups, disclosed on April 19, 2026, that a security incident had resulted in the compromise of a limited amount of customer data. The breach originated from an attacker who gained access through a Vercel employee's compromised Google Workspace account, which was itself linked to a previously breached third-party AI tool — illustrating the cascading risks of interconnected software supply chains.
What Happened
According to Vercel's disclosure, the initial attack vector was Lumma Stealer malware, which infected systems at Context.ai, a third-party AI tool used by Vercel employees. The malware harvested credentials, including an OAuth token that provided access to the Vercel employee's Google Workspace account. From there, the attacker was able to access a limited set of customer data stored within Vercel's systems.
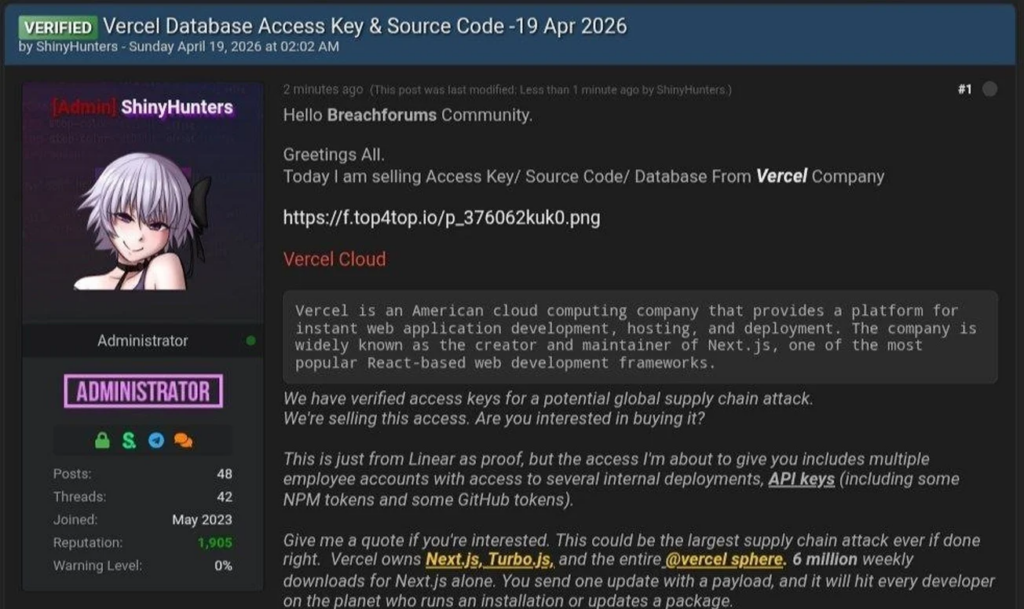
A group identifying itself as the ShinyHunters syndicate — a prolific hacking collective previously linked to major breaches at Ticketmaster, Santander Bank, and other organisations — claimed responsibility for the attack on a hacking forum. Threat intelligence analysts have noted that the claim's authenticity has not been independently verified, and Vercel has not publicly attributed the breach to any specific group.
Background
Vercel is a critical piece of infrastructure for a large segment of the AI startup ecosystem, providing hosting, deployment, and edge computing services for applications built on frameworks like Next.js. Its customer base includes thousands of AI-focused companies and developers, making it an attractive target for threat actors seeking to access sensitive data or disrupt AI development pipelines.
The ShinyHunters group has been responsible for some of the largest data breaches of recent years, typically monetising stolen data through sale on dark web forums. The group's tactics have increasingly shifted toward targeting cloud infrastructure providers as a means of accessing multiple downstream victims through a single breach.
Why It Matters
The Vercel incident is the latest in a series of supply chain attacks that have demonstrated how a vulnerability in one tool or service can create a pathway into dozens or hundreds of connected organisations. For AI developers in particular, the risks are compounded by the proliferation of third-party AI tools, APIs, and integrations that are routinely granted broad access to corporate systems and data.
What's Next
Vercel has said it has revoked the compromised credentials, notified affected customers, and is conducting a full forensic review of the incident. The company is also reviewing its policies around third-party tool access and OAuth permissions. Security researchers are urging AI companies to audit the access granted to third-party tools and to implement stricter controls on OAuth token permissions.
Sources: SWK Technologies; The Hacker News
:max_bytes(150000):strip_icc():focal(703x543:705x545)/White-House-Correspondents-dinner-042526-003-d7736c82d747408cb89cf03616114863.jpg)


